In some cases you may prefer installing Cisco VIRL on its dedicated hardware without running on a virtual machine. Most personal users do not have the luxury of access to business grade VMWare infrastructure. Some are studying for CCNA, CCNP and CCIE labs and would like to build a home lab using their existing computers. I’ve also seen businesses prefer putting VIRL on its dedicated server to achieve better performance by eliminating the VM hypervisor overhead, as well as separating it from production environment. In this session, we’ll cover Cisco VIRL installation on bare-metal standalone server.
Hardware Requirements
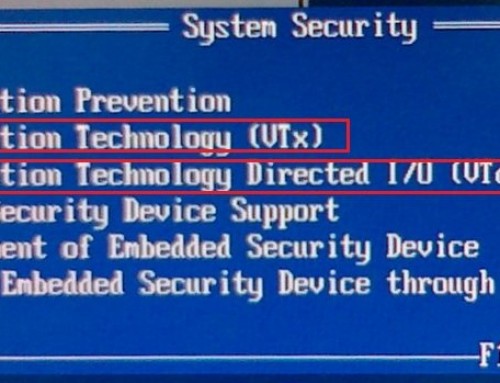
- The server must support Intel VT-X/EPT or AMD-V/RVI virtualization extensions.
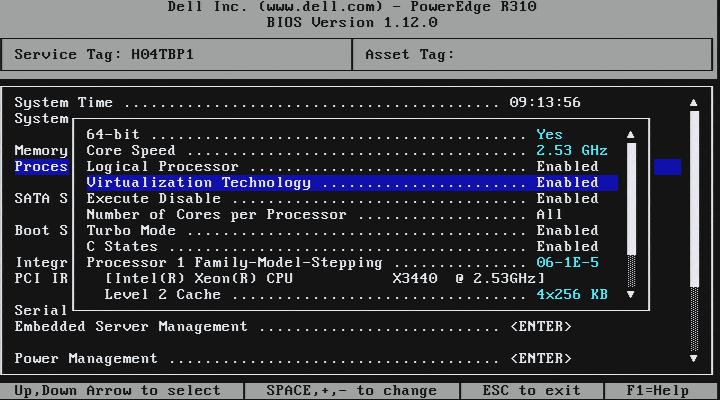
You may wonder why the hardware needs to support VT-X virtualization technology even though our Cisco VIRL installation will be on a bare-metal standalone server. VIRL in fact is also a VM host. It utilizes OpenStack technologies and each simulated router inside it is a virtual instance. What this means is that the VIRL server you deployed on your computer or dedicated server will in turn deploy virtual machines within itself. It is called nested virtualization. For this to function properly we need to be able to pass the CPU “flags” from the server to VIRL and VIRL’s virtual machine. In essence, tricking the virtual instances to think that they have direct access to the CPU. You must enable above mentioned virtualization technology in BIOS. (instructions shown later) - Minimum of 60GB hard disk space.
- Minimum 4GB of RAM.
If you need to simulate more than 10 nodes at same time, 8GB or more is recommended, 16GB or 24GB is preferred. - VIRL wants you to have five dedicated Network Interfaces (NICs).
I found you can get alone with just one, preferably two NICs and configure the rest as “dummy” interfaces. In my opinion, it is not necessary to setup five dedicated NICs since 3-5 are rarely used in most common lab setups I came across.
For demonstration, I used a Dell PowerEdge server for this tutorial. Here are its specs.
- Dell PowerEdge R310 1U Server
- Intel Xeon X3440 2.53GHz Quad Core Processor
- 24GB RAM (6x4GB)
- PERC i/6 RAID Controller
- 2x 450GB 15k RPM 3.5″ SAS Hard Drives, configured RAID1 (mirror)
Now let’s get started.
Cisco VIRL Installation on Bare-metal Standalone Server
Step 1: Obtain Cisco VIRL ISO bootable image
You can purchase a copy of VIRL license on VIRL.cisco.com. You’ll need to login with your Cisco.com account and make the purchase. You’ll receive an email with the instruction how to download the image and the license key. The ISO image is about 2.98GB. An MD5 hash sum for each package is provided along with the download link and on the download website. To avoid deploying corrupted file, make sure to verify that the hash sum of the downloaded image matches the source. The ISO image used for this tutorial was “virl.1.0.0.iso”.
- On a Mac OS X use the command “md5 filename”
- On Linux use the command “md5sum filename”
- On Windows PC, you may download the free MS File Checksum Integrity Verifier tool. Microsoft File Checksum Integrity Verifier.
Burn a DVD using the ISO image downloaded. You now have a VIRL installation DVD ready to go.
Step 2: Prepare the server for installation
Optionally, you want to run firmware update utility to update all the drivers on the server. We used Dell Repository Manager to update BIOS, RAID controller and System board drivers. This step is optional but recommended. If you are building VIRL on a used server or computer, you may want to bring all the firmware up to date to work with the current technologies.
If your server supports RAID, it is a good time to build an array to provide hard disk redundancy. In this example we configured RAID1 across two 450GB hard disks. Data are mirrored across two disks. No data lost in case one hard disk fails. RAID5 is also a very common configuration. You need to at least three hard disks to build RAID5.
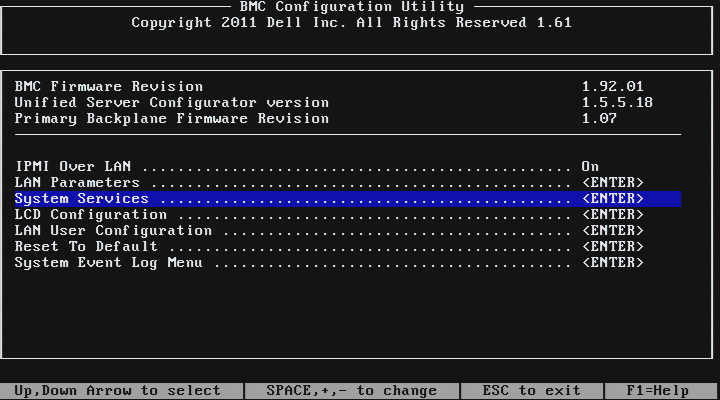
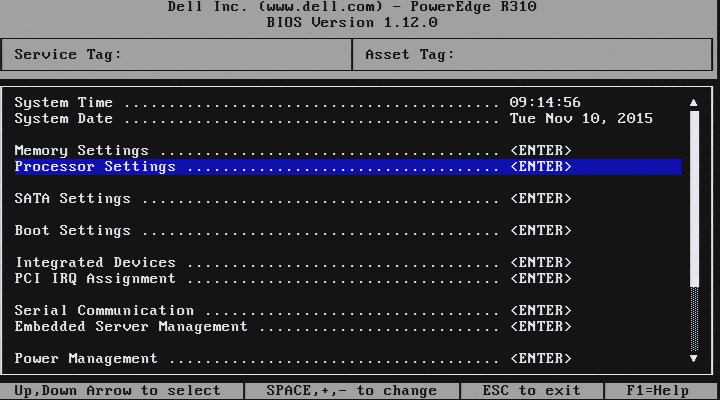
Next, “virtualization technology” needs to be enabled in BIOS. In my case it is not enabled by default. Included screenshots where to find it on the Dell PowerEdge R310.
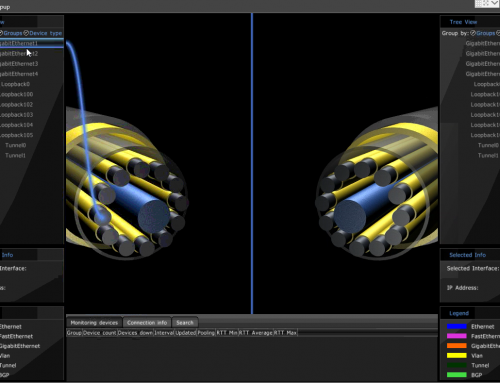
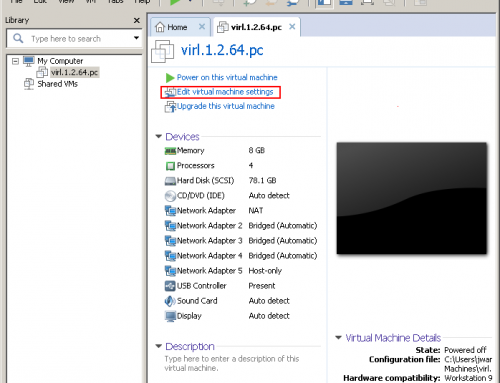
For your reference, here are some additional screenshots from other types of computers and servers. You can find in Cisco VIRL Installation on VMWare ESXi.
Step 3: Install VIRL on the server
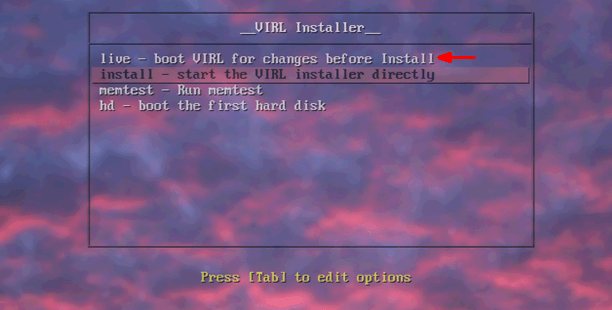
You must boot to “live – boot VIRL for changes before install” first.
VIRL needs to make changes to the default actions before actual installation. The installation will fail if you go directly to the second option “install – start the VIRL installer directly”. I have tested it and I ran into a blank screen during boot up and had to power cycle the server.

The default username / password is virl / VIRL. Once logged in, double click on “Install System to HDD” icon on the desktop and go through the wizard.
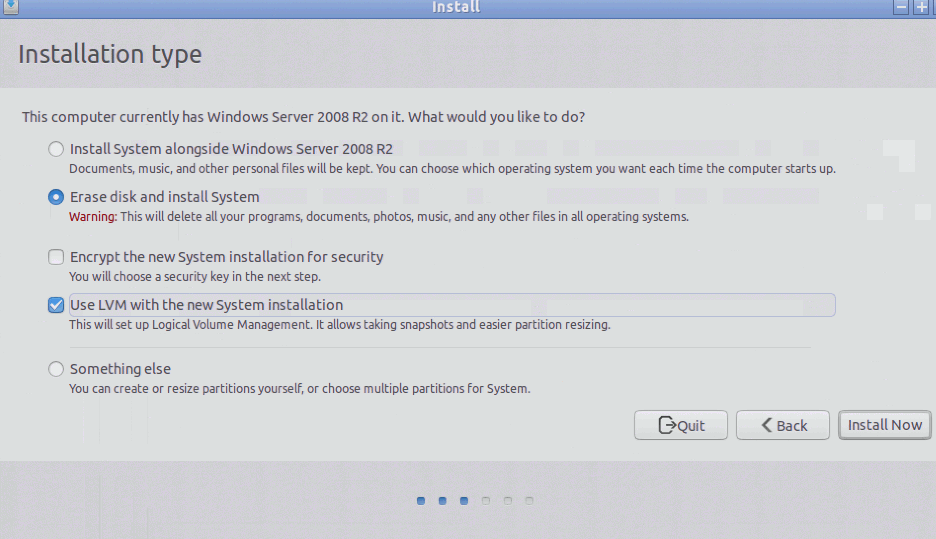
I had a Windows 2008 R2 running on the server and I am not planning to use it any more. For my installation, I’m going to have VIRL overwrite everything on my HDD and use it as a dedicated VIRL server. Do select “User LVM with the new system installation”.
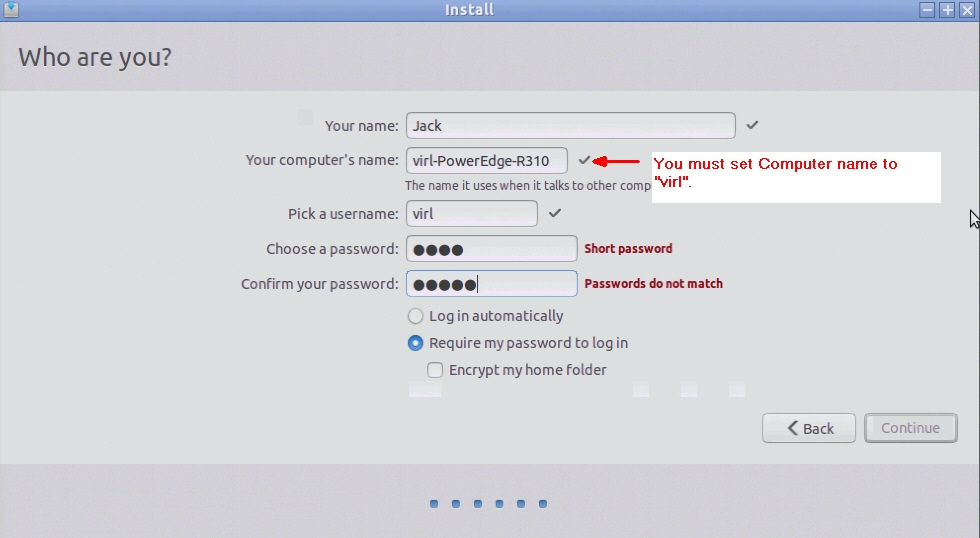
Here you are asked to enter information about the VIRL server. Be sure to change and match the following, otherwise services such as OpenStack will fail to install.
- Your computer’s name: virl
- Pick a username: virl
- Choose a password: VIRL (upper case)
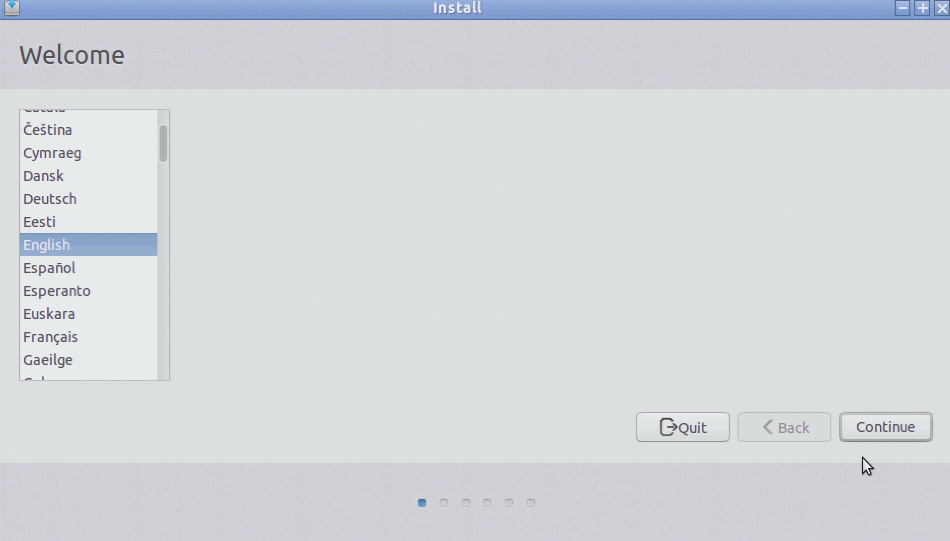
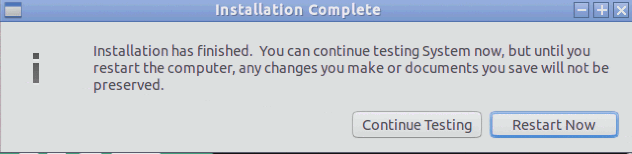
The rest of the wizard is straight forward. Select your time zone and language and start installation. VIRL will copy all the necessary files to your HDD.
This process can take several minutes. Once the installation has finished, click on Restart Now to reboot the system. Boot directly to the HDD as opposed to the DVD this time. You now have VIRL installed on your server.
Step 4: Post installation tasks
There are a few issues that need to be addressed before the VIRL server will function.
Issue 1: Replace “eth” interface descriptor with “em”.
The Ubuntu OS has changed its interface naming scheme from “eth” to “em”. The interface naming now is em1, em2, instead of eth0 and eith1. I found this version of VIRL ISO release does not have the adjustment in place. It causes the operating system fail to recognize it NIC configuration. You can see in the logs.
dmsg | grep eth shows that “renamed network interface eth0 to em1” and eth1 to eth2.
We will address the issue by editing “/etc/network/interfaces” file as well as “/etc/virl.ini”. While we are editing these files, we will assign a static IP for management. The management IP can be used to SSH to the VIRL server remotely.
sudo vi /etc/network/interfaces
Replace all “eth0” with “em1” and “eth1” with “em2”. The server does not have more than two NICs. Any other interfaces configured are irrelevant.
Create an alias for the OpenStack service address. Note that you only use “em” interface descriptor from this point.
up ip addr add 172.16.10.250/24 dev em1
Edit “em1” interface configuration, change from DHCP to static, and assign the management IP to em1. In our example, the management IP is 172.30.30.100. Here is how my /etc/network/interfaces file looked like:
auto em1 iface em1 inet static address 172.30.30.100 netmask 255.255.255.0 post-up ip link set em1 promisc on dns-nameservers 8.8.8.8 8.8.4.4 gateway 172.30.30.1 up ip addr add 172.16.10.250/24 dev em1 auto em2 iface em2 inet static address 172.16.1.254/24 netmask 255.255.255.0 post-up ip link set em2 promisc on auto lo:1 iface lo:1 inet loopback address 127.0.1.1 netmask 255.0.0.0 auto lo iface lo inet loopback
Next we need to edit /etc/virl.ini file by replacing “eth” with “em”, and adding “dummy” interfaces.
Search for the following lines of configuration and match them with this:
public_port: em1 using_dhcp_on_the_public_port: False l2_port: em2 l2_port2: dummy0 l3_port: dummy1 dummy_int: True internalnet_port: dummy2
Save the file and reboot server. “sudo reboot now”.
Once the server has rebooted, we should be able to SSH to the server using its management IP 172.30.30.100. However I encountered the issue below preventing me from logging in remotely.
Issue 2: Could not SSH to the VIRL server. “Connection reset by peer”.
I troubleshot the issue by monitoring the server’s log file while attempting to SSH.
tail -f /var/log/auth.log
Add -v to get a verbose output at the client end.
ssh [email protected] -v
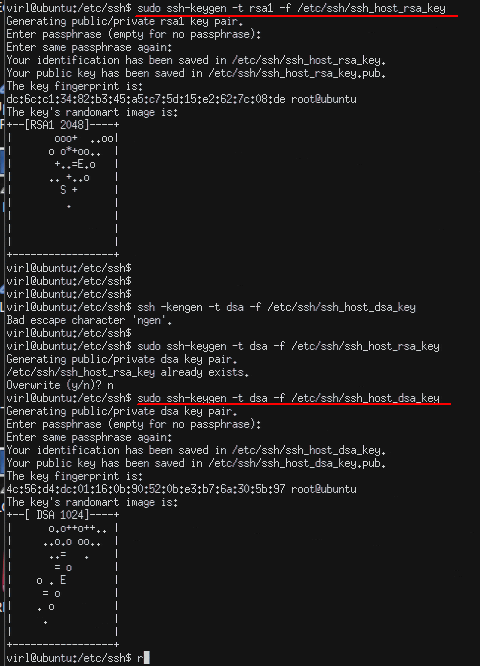
This might give you more details about the cause. In my case the rsa and dsa keys are missing or mismatch on the server, fixed them by recreating rsa and dsa keys on the VIRL server. Go to the VIRL server and open Terminal, and issue the following commands.
ssh-keygen -t rsa1 -f /etc/ssh/ssh_host_rsa_key ssh-keygen -t dsa -f /etc/ssh/ssh_host_dsa_key
Here is a screenshot how it looked like on my server.
Once the RSA and DSA keys are regenerated, you should be able to log in the server remotely using SSH.
Issue 3: “nova service-list” and “neutron agent-list” will not work.
If you had tried installing VIRL by following Cisco’s official documentation, you may find neither of these verification would work. You must make sure NTP server is working and finish VIRL activation before the verification commands would work. You may skip this step and move on to the next.
Step 5: Preparing for VIRL activation
Confirm KVM acceleration can be used by running this verification command.
virl@ubuntu:~$ sudo kvm-ok INFO: /dev/kvm exists KVM acceleration can be used
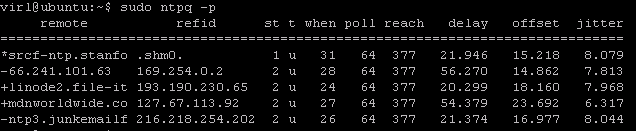
For VIRL activation to work, NTP serivce must be running and time has to be synced.
Edit /etc/ntp.conf and replace “eth0” with “em1”.
interface listen em1
Restart NTP service.
virl@ubuntu:~$ sudo service ntp restart * Stopping NTP server ntpd [ OK ] * Starting NTP server ntpd [ OK ]
Give it a few minutes for NTP service to talk to the time servers and synch with them. Run “sudo ntpq –p” to confirm that the NTP server is talking to the time servers and the local time has been synched with one of them with asterisk (‘*’). Display the current time using command “sudo date”.
Step 6: Activate VIRL
From this point, you can reference Cisco VIRL Installation on VMWare ESXi, Step 7: License Activation. The process is the same.
In this session, we’ve covered Cisco VIRL Installation on Bare-metal Standalone Server. If you have any questions regarding the content, feedback or suggestions for future topics, please leave a comment below. I’d love to hear from you!


Jack,
I recently ‘stumbled’ across your nice blog whilst doing some research on VIRL.
I think your articles are containing the most valuable information re the VIRL installation I found so far. Many thanks for sharing.
I am planning to run VIRL on a bare-metal standalone server. Well, it is not really a server hardware, but something nearby… 😉
I’ve got a HP Z600 workstation with 2 x Intel Xeon processor E5620, 2.40 GHz, 12 MB cache, 1066 MHz memory, Quad-Core and 48 GB of RAM.
Based on your experience, would you think that box will be strong enough to run VIRL Personal Edition to its full extent?
Cheers.
—
U.
You have plenty of RAM and a good CPU. The only thing you need to verify is that if your CPU supports VT-x/EPT virtualization technology.
Reference Intel and AMD’s websites and verify if your CPU model has virtualization support.
http://www.intel.com/content/www/us/en/support/processors/000005486.html
I also have the most common issues you may run into summarized here:
https://www.speaknetworks.com/cisco-virl-installation-troubleshooting-common-issues/
Jack,
many thanks for your swift response.
Luckily http://ark.intel.com/products/47925/Intel-Xeon-Processor-E5620-12M-Cache-2_40-GHz-5_86-GTs-Intel-QPI says ‘Intel® VT-x with Extended Page Tables (EPT) = Yes’. So based on this I should be fine. 😉
Again, many thanks.
Cheers.
—
U.
This post was the end of the road for a day of frustration. I spotted the issue with “em1” vs “eth0” right away. But I couldn’t put the pieces together for the nested virtualization, and where the changes needed to be made. Thanks for this post
Glad it was helpful.
Very good write-up. Solved a few issues for me as well. Did you have any other issues (activation, services not starting, etc)?
hi Lee,
I did ran into some issues that certain service won’t start until SALT is configured. It did take several tries for VIRL to contact the SALT server. Other than that all went well.
Hi Jack, I read your book and write here, I was able to edit the virl.ini file but I am having issue editing the interfaces file. I login as virl/VIRL and open the interfaces file and edit the eth to em but when I try to save the file I get permission issue.
Habib, you’ll need to use the “sudo” command when editing the interface file. “sudo vi /etc/network/interfaces”. Password is VIRL.
Hi Jack, Thanks for this post it helped me in installing VIRL. Now, I am stuck at this issue
Agent “neutron-linuxbridge-agent” (host “virl”) is not up. Could you please tell me what i am missing here?